Today’s Big Stories
***Zoom’s Fall From Grace***
Thanks to the coronavirus, the past weeks and months have been a whirlwind for just about everyone. That’s especially so for the video conferencing company Zoom, which has seen one of the fastest explosions and sudden fall from grace of any company in recent memory. Zoom’s user base has exploded in recent weeks with the majority of US and European workers forced to abruptly pivot to remote working alternatives in the wake of COVID-19 social distancing guidelines. With the majority of companies forced to start working remotely nearly overnight, millions of users flocked to video conferencing apps to keep their operations online. Of all the companies welcoming work from home-ers in, Zoom by far came out on top.
Then, the house of cards began to crumble.
The past month has seen Zoom plagued by a streak of privacy scandals, lies spewing from the top of the company, and mass exodus’ from the platform by companies, and even entire countries. All of that led global wealth management companies to downgrade Zoom to “underperform,” which is the equivalent of a sell rating.
It’s possible that many of you have turned to Zoom for work recently, so its worth exploring just what went wrong.
On last week’s newsletter, we discussed some of the first cracks in the now clearly weak Zoom armor. First, news broke that Zoom had accident leaked the emails and phone numbers of over 1,000 of its users. The data leak, according to VICE, occurred as a result of Zoom’s “Company Directory” setting, which automatically adds people to a user’s contact list if their email has a matching domain name. While this was meant to help people in the same company, using the same domain, connect seamlessly, many users claimed they signed up using personal emails and Zoom grouped them together with complete strangers.
That same week, Zoom was hit with a class-action lawsuit from a customer claiming the company violated her privacy when it sold some of her personal data to Facebook. That data allegedly includes the person’s person’s device model, time zone, phone carrier, and their unique advertiser identity. While the practice of selling this type of data, especially to behemoths like Facebook, isn’t all that unusual, it was the first real indication of Zoom’s complicity in the greater corporate surveillance for-profit network. Remember, Zoom has branded itself as a privacy-focused company.
So that’s all pretty bad, but in the grand scheme of callous start-up privacy fuck ups, some could probably write these off as mere growing pains ... but then came the schools.
Like other institutions, schools, ranging from college-level classes down to the elementary level turned to Zoom. For many of these video calls where links were shared for entry, those virtual conference rooms were public, a fact sometimes unknown to college professors and high school teachers. Reports started pouring in all around the country of algebra classes and literature courses being broken into by trolls yelling profanities, displaying pornography, shouting racial slurs, and doing just about anything they could to ruin a call. The troll hijacking became so commonplace that a new word was created for it: Zoombombing.
The string of Zoombombings drew the ire of legislators nationwide, like New York Attorney General Letitia James who sent a letter to the company probing it over its privacy protections. Issues with Zoombombing got so bad that the FBI even issued an alert:
“As large numbers of people turn to video-teleconferencing (VTC) platforms to stay connected in the wake of the COVID-19 crisis, reports of VTC hijacking (also called “Zoom-bombing”) are emerging nationwide, “ the alert reads. “The FBI has received multiple reports of conferences being disrupted by pornographic and/or hate images and threatening language.”
The FBI alert went on to cite examples of trolls hijacking classroom videos in Maine and Massachusetts, yelling profanities, and in one case, flashing a swastika tattoo.
In an attempt to pour water on the raging PR firestorm, Eric Yuan, Zoom’s CEO, went on CNN and told Brian Stelter the company made some “missteps,” and may have “moved too fast.”


Those apologetic words fell largely on deaf ears. In the wake of the school privacy controversy, multiple school districts around the country, including those in New York City, have banned the use of Zoom for remote learning.
But annoying pranks are the least of Zoom’s problems. While Zoom had marketed itself as coming equipped with peer to peer encryption, an investigation by The Intercept found that the company still had access to unencrypted video and audio from meetings. In other words, not peer to peer encrypted.
Another investigation in the company by Zoom found pervasive security vulnerabilities in the company’s “waiting room” feature and, more damning, found potential links to the Chinese surveillance state.
While Zoom is a Silicon Valley startup, that same Citizen Lab investigation found that the company runs many of its servers out of China. Zoom also owns three separate Chinese companies which, according to the report, it uses to mine labor for Zoom. In an act described by Citizen Lab as labor arbitrage, Zoom essentially uses these alleged 700 Chinese workers to avoid paying US wages while simultaneously selling to US customers.
Of course, that practice isn’t unique (just look at the fashion industry) but being a tech company holding potentially sensitive personal information, Zoom’s on the ground Chinese ties can leave them, and its user's data subject to Chinese surveillance policies. Tech companies like Google and Shutterstock have made headlines in recent years for similar privacy issues resulting from their involvement in Chinse markets. The Citizen Lab report ultimately concluded that Zoom was “not suited for secrets.”
And it’s not just schools bailing on Zoom. Google, the entire US Senate, NASA, and Tesla, all issued statements in the past week ago announcing they would no longer use Zoom due to privacy concerns. Adding insult to injury for Zoom, offices in Taiwan said effectively banned government officials from using the service.
“During this COVID-19 crises we moved too fast,” Yuan said in his recent CNN interview. Yet, according to most of the reporting released in recent weeks, some of the most pervasive issues associated with Zoom predate the Coronavirus and are not issues of scale, but rather elements built into the foundation of the company from the ground up.
With all of this drama popping up, is worth considering how Zoom became the “top dog” of video conferencing in the first place. There are plenty of other options out there, like Microsoft Teams and Houseparty. I mean, remember Skype?
If you are going to keep using Zoom during the shutdown, here are a few security tips laid out by the indefatigable, (and not without its own controversy) Kaspersky Labs.
Like what you’ve read so far? If so, please consider becoming a paid subscriber for $5 per month.
If that’s too much commitment, no worries. You can also support the newsletter by making a one-time Venmo donation to @Mack-DeGeurin to help keep this content coming.
***Virus Tracking Fears Gain Added Legitimacy***
Last Friday’s newsletter noted how over 100 civil liberties and civil rights groups signed a joint statement decrying unrestricted coronavirus related surveillance. The piece also noted that two major voices were missing from the list— the ACLU and the Electronic Frontier Foundation. Well, as of Wednesday, both organizations have come out swinging against America’s new age of surveillance.
In a report released on Wednesday, the ACLU urged the public and legislators to approach any new tracking efforts with extreme caution, and said any use of personal data,” should be temporary, restricted to public health agencies and purposes, and should make greatest possible use of available techniques that allow for privacy and anonymity to be protected even as the data is used.” You can read all of the potential dangers they warn about here.
At the end of last week, the EFF released its own guidelines in response to the surge in companies attempting to profit off of coronavirus tracking. Their call for caution echoed many of the fears raised by the ACLU.
“Even if the government shows that a surveillance power would be effective, EFF still opposes its use if it would too greatly burden our freedoms. High-tech surveillance can turn our lives into open books. It can chill and deter our participation in protests, advocacy groups, and online forums. Its burdens fall all too often on people of color, immigrants, and other vulnerable groups.”
On Tuesday, the EFF went a step further and released a blog post objecting to the use of thermal cameras to detect fevers. In some areas of the world, like China and South Korea, thermal cameras have been used at entrances to transit station, restraints, and bars to quickly tell whether or not someone might be sick, Avocated for these cameras point to their use as a way to potentially move away from social distancing while limiting the spread of the virus. That, however, is an unreasonable trade-off according to the EFF.
“These cameras threaten to build a future where public squares and sidewalks are filled with constant video surveillance—and all for a technology that may not even be effective or accurate at detecting fevers or infection,” the EFF wrote on its website.
Aside from the dystopian optics, the groups warned the proposed cameras could, “outlive their [their] usefulness” and be used to chill free expression, movement and association.
They weren’t the only ones weighing in. In an analysis piece released Tuesday for Brennan Center for Justice, Ángel Díaz succinctly summarized the innermost ways this sudden embrace of geolocation tracking data rubs up against personal liberties. The entire piece is worth reading, but about halfway through Díaz drew up a comparison made in the newsletter several weeks ago and one that has since gained some mainstream use. Society’s sudden, fear-based embrace of surveillance, Díaz argued, resembles in many ways the same concessions made by Americans immediately following the September 11 terrorist attacks. Here’s Díaz:
“Our experience with expanded surveillance after 9/11 provides an object lesson. With the laudable-sounding goal of preventing the next terrorist attack, the government secretly undertook new dragnet surveillance programs that violated Americans’ privacy rights. The hasty rollout also sacrificed necessary assessments of whether these programs were likely to work.”
“Years later, government analyses found that mass data collection for counterterrorism purposes was ineffective. The Department of Defense, for example, found that machine learning systems were unable to “accurately anticipate” terrorist threats. Furthermore, this data collection was actually counterproductive, because it ended up burying useful intelligence. Even with a dismal success rate, many of the post-9/11 surveillance programs are still active today, nearly two decades after the emergency that was used to justify their inception.”
While Díaz acknowledged potential merits to limited, anonymized tracking, he went on to echo another concern raised in this newsletter — that of surveillance companies operating in the shadows.
“The government’s discussions with the companies who hold this data, however, have been conducted quietly and behind closed doors. This secrecy is a problem in itself. It also suggests that the government may be interested in collecting data simply in the hope that it will be helpful, but without a clearly effective plan in place.”
So far in the United States, the most prolific and far-reaching attempts at coronavirus tracing were not made public by a presidential press briefing, a tech company spokesman, or a nationwide alert, but rather through investigative reporting revealing practices of surveillance that otherwise would have remained veiled in darkness.
In Other News…
***Twitter’s sharing more data with advertisers***
Twitter users logging onto the website on Wednesday were greeted with an unwelcome new notification with the title, “An update to your data sharing settings.” Over the course of the paragraph, the app would explain that the “update” to data sharing settings was more akin to a relinquishing of data sharing settings.
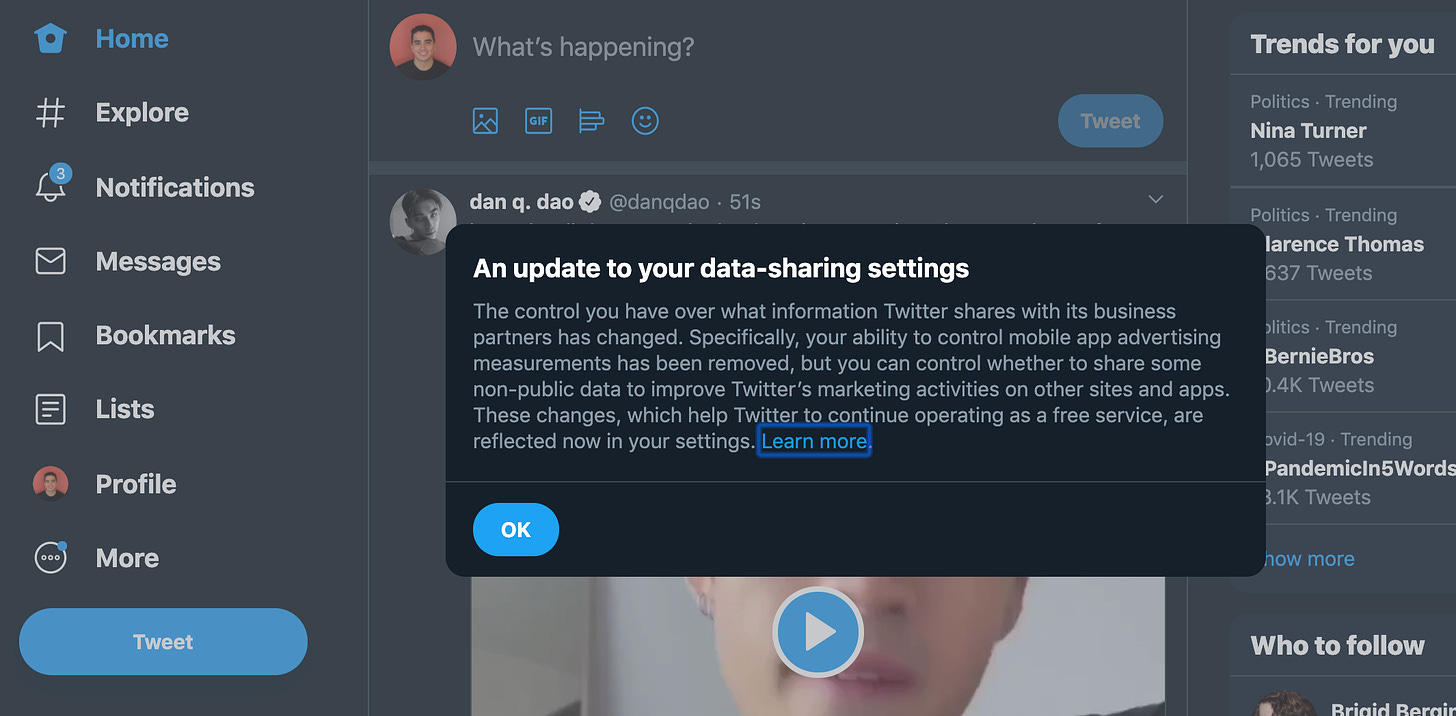
“Specifically, your ability to control mobile app advertising measurements has been removed,” the notification reads, “but you can control whether to have some non-public data to improve Twitter’s marketing activities.
Prior to today, Twitter offered a useful tool that allowed users to opt of sharing private data with advertisers. With that feature on, Twitter couldn’t’ share the ads you viewed on your phone, or your phone’s unique tracking identified, with advertising companies. That’s been axed.
Here’s the Verge’s Jacob Kastrenakes explaining the privacy changes further:
“An option in Twitter’s privacy settings called “Share your data with Twitter’s business partners” used to let you disable sharing of this information. That setting still exists, but Twitter now says it has removed your control over “mobile app advertising measurements.” Disabling the setting can still prevent sharing of other information, such as your interests. Other Twitter privacy settings, like disabling web tracking, are still available. Twitter will not share your name, email address, phone number, or username.”
The reason for the change, in tech company talk, was, “to help Twitter operating as an ad-free service.” In other words: money.
There’s one major exception to this change and that’s users in Europe. Thanks to GDPR regulations that require advertisers obtain consent before collecting personal information, Twitter users in Europe and the United Kingdom will have to opt-in before Twitter can hand over data.
***China’s coronavirus surveillance***
Wuhan’s coronavirus lockdown was lifted this week, but surveillance continues on. This week marked a pivotal moment for the coronavirus worldwide. After months of strict lockdown, marked by travel restriction and some of the most intense daily surveillance yet seen during the pandemic, residents of Wuhan province were allowed to leave and resume some semblance of normal life. While Wuhan’s battle against coronavirus may be diminishing, some of its new surveillance practices remain.
In an effort to supposedly prevent a second wave of coronavirus cases form reemerging, the Chinese government is reportedly controlling the movements of residents through specially designed software installed on WeChat and Alipay. Residents reportedly fill out a health survey on the apps and are then assigned a color of green, yellow, red, which tells them whether or not they can leave their home and where they are allowed to travel.
It's not just Wuhan using the health color codes either. According to Business Insider, over 200 Chinese cities are following the same measures.
The continued surveillance in areas of China past the “end” of coronavirus concerns may provide a peek into the future for other nations embracing tracking technology.
Sophia Ankel, Business Insider
***Facebook ramps up coronavirus monitoring***
Facebook announced it is developing new location tracking tolls to determine whether or not users are adhering to social distancing guidelines. Called, “The Disease Prevention Map,” Facebook says the tools are meant to “ help public health organizations close gaps in understanding where people live, how people are moving, and the state of their cellular connectivity, in order to improve the effectiveness of health campaigns and epidemic response.”
Facebook claims the maps will include co-location data that can determine the probability users in one area will come in contact with one another, movement range trends to show how much users are moving on a regional level, and a social connectedness index that “data reveals friendships across states to show the areas where people might need more support.”
Like most tech companies tossing their hat in the coronavirus tracking ring, Facebook clams the data it’s using is anonymized and that the company won’t use the patterns to track individuals.
“We think that Facebook and the wider tech industry can continue to find innovative ways to help respond to that crisis,” a Facebook spokesperson told CNBC. “But we don’t think the help entails compromising privacy.”
***Kids sue Google***
Two Illinois children are suing Google after alleging the company illegally collected face scans and other biometric data on millions of kids. The lawsuit was filed in a federal court in San Jose, California and the two children were identified only by the initials H.K. and J.C.
The suit accused Google of creating “face templates” and “voiceprints” through the mass collection of Chromebook data. Last month, this newsletter divided into similar allegations made by the state of New Mexico, which accused the tech giant of “spying” on children. As noted there, Google has spent the past decade filling classrooms all around the country with their Chromebook laptops. Under the Children's Online Privacy Protection Act, Google is legally prevented from selling data on children under the age of 13 to advertisers. The company has been far from perfect on this point.
Here I’m quoting directly from the most recent lawsuit:
"Google has complete control over the data collection, use, and retention practices of the 'G Suite for Education' service, including the biometric data and other personally identifying information collected through the use of the service, and uses this control not only to secretly and unlawfully monitor and profile children but to do so without the knowledge or consent of those children's parents.”
***Did Facebook try to buy a Surveillance Mercenary?***
Spyware for hire company NSO Group claims Facebook tried to buy the company out in 2017. NSO Group is an Israeli spyware firm that has made headlines in recent years after multiple investigations found that its Pegasus spyware tools have been used by Mexican drug cartels, and were used to track and ultimately assassinate Saudi Arabian journalist Jamal Khashoggi.
The accusations from NSO Group come amidst as a side effect of an ongoing legal battle between the spyware company and the social media behemoth. That larger battle stems from an October 2019 lawsuit filed by Facebook which accused NSO Group of facilitating a hack of several prominent WhatsApp users (WhatsApp is owned by Facebook) on the behest of unnamed governments.
Long Reads/ Food for Thought
The Technology That Could Free America From Quarantine
By Derek Thompson for The Atlantic


Pandemic Data-Sharing Puts New Pressure on Privacy Protections
By Ben Brody and Naomi Nix for Bloomberg News

And last but not least …
Standard scientists design a toilet that using facial recognition for your butthole
Thom Dunn, for Boing Boing
Uh...yeah, that’s right. Apparently it measures “analprints”




